Electronics | Free Full-Text | A Generative Model for Traffic Demand with Heterogeneous and Spatiotemporal Characteristics in Massive Wi-Fi Systems
Sustainability | Free Full-Text | A Review of Monitoring Technologies for Solar PV Systems Using Data Processing Modules and Transmission Protocols: Progress, Challenges and Prospects
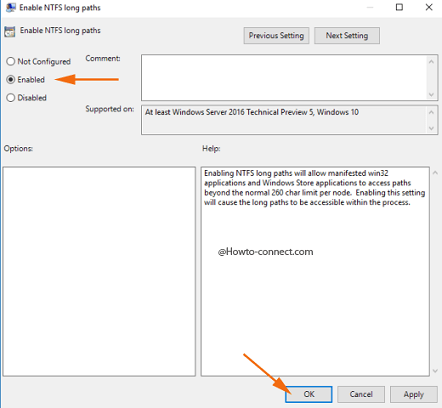
![ERROR: [Common 17-143] Path length exceeds 260-Byte maximum allowed by Windows: <LongPathtoFileName> : r/FPGA ERROR: [Common 17-143] Path length exceeds 260-Byte maximum allowed by Windows: <LongPathtoFileName> : r/FPGA](https://preview.redd.it/liwpya11xjf21.png?width=509&format=png&auto=webp&s=6b0eb6263a4c18acc14b975a5b86c639984653a4)
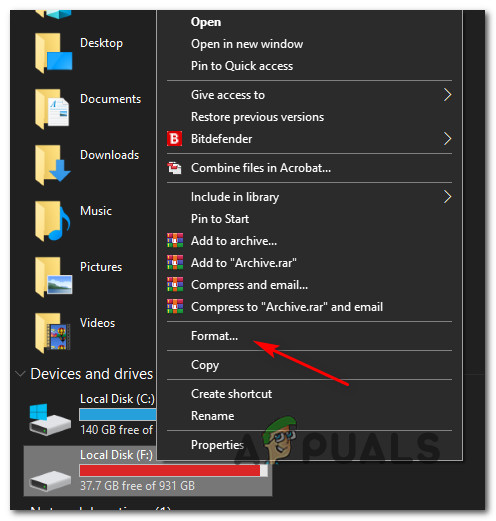
ERROR: [Common 17-143] Path length exceeds 260-Byte maximum allowed by Windows: <LongPathtoFileName> : r/FPGA
Cryptography | Free Full-Text | Power Side-Channel Attack Analysis: A Review of 20 Years of Study for the Layman

A survey on blockchain cybersecurity vulnerabilities and possible countermeasures - Hasanova - 2019 - International Journal of Network Management - Wiley Online Library
![SOLVED ] 🔥Error File Size Exceeded the Maximum Size Permitted by PHP Configuration 100% 👌Working - YouTube SOLVED ] 🔥Error File Size Exceeded the Maximum Size Permitted by PHP Configuration 100% 👌Working - YouTube](https://i.ytimg.com/vi/qsQUV0cFfcA/maxresdefault.jpg)





![4. Serial Communications - Arduino Cookbook, 2nd Edition [Book] 4. Serial Communications - Arduino Cookbook, 2nd Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781449321185/files/httpatomoreillycomsourceoreillyimages1673040.png)